The U.S. Power Grid’s Cyber War Games
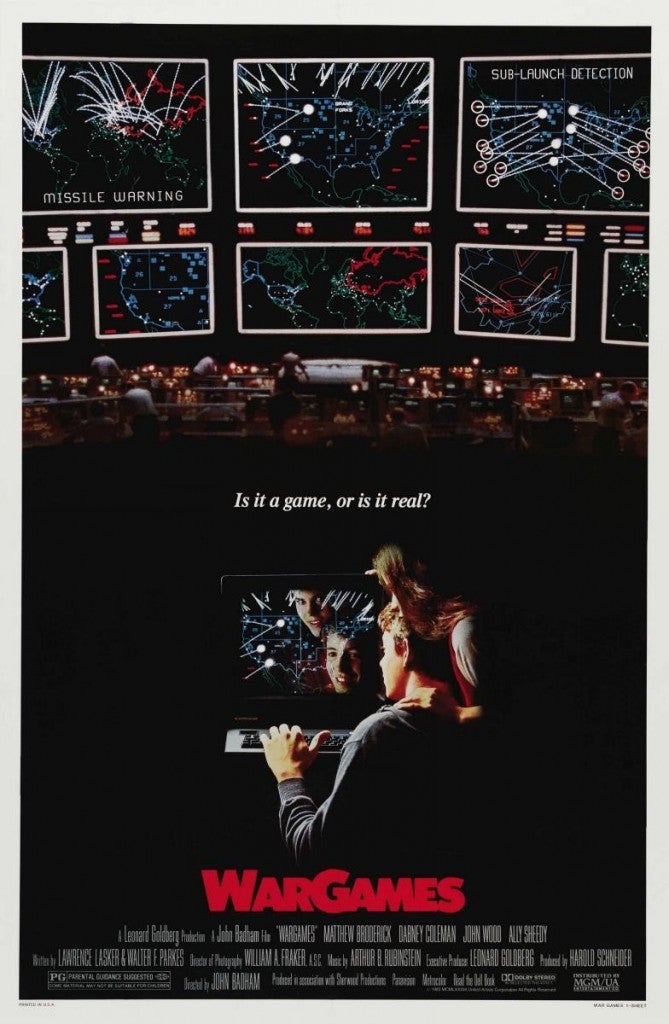 In the 1983 thriller WarGames, Matthew Broderick plays a teen-age computer geek who unknowingly signs onto a Pentagon computer while hacking into a toy company’s new computer game. Thinking that he’s simply playing a game called Global Thermonuclear Warfare, Broderick launches the game and nearly starts a nuclear war. The North American Electric Reliability Council (NERC) will hold its own war game next month with a simulated attack on the U.S. power grid.
In the 1983 thriller WarGames, Matthew Broderick plays a teen-age computer geek who unknowingly signs onto a Pentagon computer while hacking into a toy company’s new computer game. Thinking that he’s simply playing a game called Global Thermonuclear Warfare, Broderick launches the game and nearly starts a nuclear war. The North American Electric Reliability Council (NERC) will hold its own war game next month with a simulated attack on the U.S. power grid.
The drill, called GridEx II, will take place on November 13-14 of this year. The participants will include 65 utilities and eight regional transmission organizations, representing most of the nation’s electricity customers. The drill will test how well the electric utility industry and the grid itself respond to physical and cyber attacks.
A NERC Critical Infrastructure Protection Committee (CIPC) working group will begin the drill by sending participants a series of simulated physical and cyber attacks, climaxing in a national security emergency. Participants will then respond and interact with each other, just as they would in a real emergency. The simulation will last 36 hours, and the CIPC working group will evaluate the participants’ responses and provide feedback on how their actions impact the ongoing scenario. After the drill, the working group will analyze the results and prepare a report on lessons learned.
The drill is timely. Our nation’s power grid is under constant cyber attack, according to a survey of electric utilities by U.S. House Representatives Henry Waxman and (now Senator) Edward Markey. James Clapper, the Director of National Intelligence, described cyber attacks as a soft war that is already underway and a dire global threat in his April 2013 World Threat Assessment of the US Intelligence Community. The Department of Homeland Security investigated over 200 serious cyber attacks against critical facilities during the first half of 2013, and more than half of these targeted the grid.
Adequate Investment
The U.S. has developed a number of cyber security protections for the grid, but we must do more. Our country needs to make adequate investments in cyber security. With the huge budget deficits that the U.S. has incurred in recent years, the proper level of government spending is often at issue. Given the devastating consequences of a cyber attack on the grid, this is one area where we can’t afford to cut corners. Our leaders must ensure that federal budget cuts do not impair the Department of Energy’s and the Department of Homeland Security’s means to protect our nation’s critical energy infrastructure from cyber attacks.
Broader FERC Authority
 We also need legislation granting the Federal Energy Regulatory Commission (FERC) broader authority to protect against cyber attacks. FERC is charged with protecting the grid against cyber attacks, but it doesn’t have the legal authority it needs to do so. FERC has pleaded with Congress to fix this oversight.
We also need legislation granting the Federal Energy Regulatory Commission (FERC) broader authority to protect against cyber attacks. FERC is charged with protecting the grid against cyber attacks, but it doesn’t have the legal authority it needs to do so. FERC has pleaded with Congress to fix this oversight.
The Federal Power Act grants FERC authority over the bulk power system, but most of the smart grid equipment that creates vulnerabilities is installed on local distribution systems beyond its jurisdiction. As a result, the National Institute of Standards and Technology (NIST) has put together a three-volume set of smart grid cyber security standards – but these standards are voluntary. FERC is working with the National Association of Regulatory Utility Commissioners to monitor whether utilities are following these voluntary standards, but this is not enough. The threat of grid cyber attacks is too real, and the potential consequences too dire. The NIST standards should be mandatory and FERC’s authority should extend to critical distribution infrastructure that puts the bulk power system at risk.
Any new legislation should empower FERC to act proactively. FERC should have the means to take timely actions to counter clear and present dangers as they arise. Unfortunately, NERC’s process for adopting cyber standards is slow and unwieldy. Because FERC’s present jurisdiction is passive in nature, it can only approve standards developed by NERC. Congress should expand FERC’s authority to act in case of emergency.
Coordinated Enforcement
The appropriate boundary between federal and state control over electricity service has been disputed for over a century, since Thomas Edison’s day. And, until recently, the manner of providing electric service had not changed much since Edison’s era. The smart grid is beginning to modernize our energy infrastructure by marrying the Internet to the electric grid. Just as the Internet is a matter of interstate commerce, so are critical smart grid facilities that could disrupt the bulk power system. We can ease jurisdictional tensions by following an existing model that uses a federal-state partnership to enforce federal standards – interstate pipeline safety.
Interstate pipeline safety standards are established by the Pipeline and Hazardous Materials Safety Administration (PHMSA), a branch of the Department of Transportation. Although the PHMSA sets the standards, any state can assume responsibility for enforcing them within their borders. The state simply needs to follow the federal standards at a minimum and apply the same enforcement penalties. While not perfect, this federal-state partnership has generally succeeded in ensuring pipeline safety in a cost-effective manner.
Information Sharing
We also need legislation to enable better practices for sharing information about cyber threats. At the moment, we have two venues where the government and utilities voluntarily share this information:
- the Department of Homeland Security National Cybersecurity and Communications Integration Center (NCCIC); and
- the NERC Electricity Sector – Information Sharing and Analysis Center (ES-ISAC).
Perhaps a better approach would be to establish a new, independent organization to act as a single clearinghouse for cyber security threats. Today, government agencies share alerts and notifications about impending cyber threats. But the information often fails to provide sufficient detail for the private sector to take action.
Government employees should be allowed to share sensitive details as necessary, to protect against a cyber attack. As a matter of security, the utility personnel who receive this information should be screened for the appropriate level of national security clearance. If electric utilities are required to share confidential information, it should not be disclosed beyond these groups. Many of these concerns are addressed in the Cyber Intelligence Sharing and Protection Act of 2013. The House passed this bill on April 18, 2013 by a 288-127 vote. The Senate should pass this bill too.
Electric Utility Commitment
Finally, utilities should commit to following cyber security best practices, rather than doing the bare minimum. NERC publishes voluntary cyber security recommendations, but only 20% of electric utilities follow these recommendations. Utilities seek to provide safe, adequate and reliable service in a cost-effective manner. They should add cyber security to this credo. To facilitate this, state utility commissions should allow timely recovery of cyber security costs.
Hopefully, NERC’s war game simulation will have a happy ending like the 1983 film. If we don’t do more to strengthen our vulnerable grid’s cyber security, we could be writing our own screenplay for a disaster movie.